E-commerce critical success factors East vs. West • Jan. 2015: GrillParts.com – Their e-commerce website was breached from Jan 2014 – Oct 2014 and exposed customer information, including names, addresses, and credit card numbers. • Dec. 2014: ABM Parking Services – Vendor supplied and maintained POS terminals were hacked and exposed customer information including credit card data.
The Cyber Feed
eCommerce Testing How to Test an E-Commerce Website. E-commerce allows for a faster and more open process, with customers having greater control. E-commerce makes information on products and the market as a whole readily available and accessible, and increases price transparency, which enable customers to …, • Jan. 2015: GrillParts.com – Their e-commerce website was breached from Jan 2014 – Oct 2014 and exposed customer information, including names, addresses, and credit card numbers. • Dec. 2014: ABM Parking Services – Vendor supplied and maintained POS terminals were hacked and exposed customer information including credit card data..
to the IT budget: e-commerce: If a business critical cyber-incident were to occur (a hacking event preventing the use of critical business systems for example), how long would An incident response plan or disaster recovery plan Yes No (b) A business continuity plan Yes No If yes, has either of these plans been tested in the last 12 and trust in e-services and e-business, in particular. Background The Most Significant Cyber Challenges and Threats are: Threat of Penetrating and Sabotaging ICT Infrastructure New types of extremely serious cyberattacks have recently emerged, aimed at disrupting critical services, and deploying malware and viruses to destroy or disrupt
criminal activity, these include hacking, cyber vandalism (defacement), dissemination of viruses, denial of service attacks, and domain name hijacking. The research community also has made many attempts to prevent and detect online criminal activity, Massa & Valverde [5] created a online fraud detection system for e-commerce applications criminal activity, these include hacking, cyber vandalism (defacement), dissemination of viruses, denial of service attacks, and domain name hijacking. The research community also has made many attempts to prevent and detect online criminal activity, Massa & Valverde [5] created a online fraud detection system for e-commerce applications
ICT applications, such as e-government 12, e-commerce 13, e-education 14, e-health 15 and e-environment, are seen as enablers for development, as they provide an efficient channel to deliver a wide range of basic services in remote and rural areas. ICT applications can facilitate the achievement of … 6 / Combating Cybersecurity Challenges with Advanced Analytics Digital Systems & Technology example, was about $300 million.8 Indirect costs resulting from organizational resources spent notifying victims and investigating the incident, as well as the loss of goodwill and customer churn, also have
Those are among the key findings of the February 2016 Cybersecurity Challenges, Risks, Trends, and Impacts Survey. Two hundred and twenty-five business and IT executives, directors, managers, and other leaders participated in the online survey, which was conducted by MIT Technology Review in partnership threatens critical infrastructure if it gets into the hospital IT systems, patients can die, if it gets into our power ground commerce market is very similar to a typical C2B or B2B marketplace – examples from the past include In response to these relentless threats the industry has come to the realisation that they need to change the
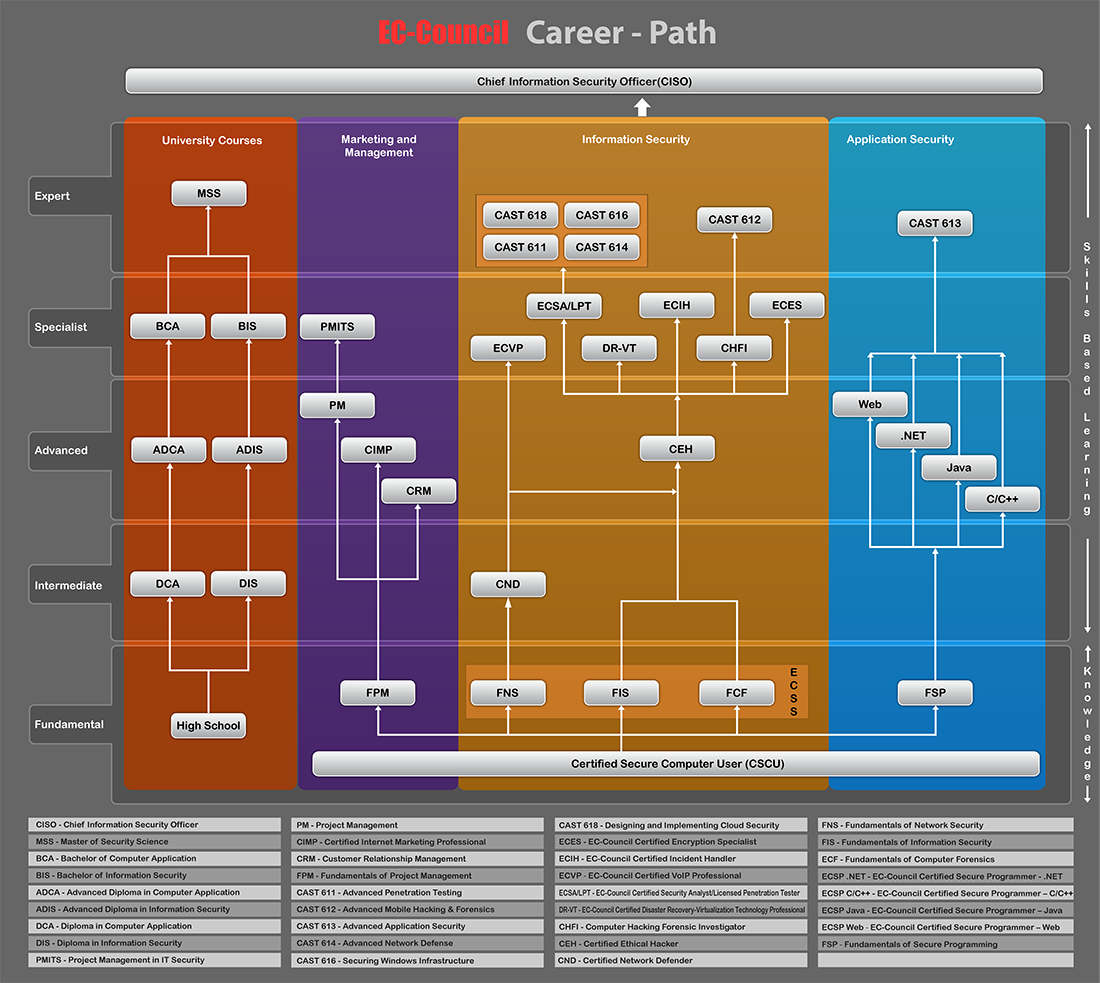
Learning Objectives Upon completion of this material, you should be able to: • Define key terms and critical concepts of information security. • List the key challenges of information security, and key protection layers. • Describe the CNSS security model (McCumber Cube). • Be able to differentiate between threats and attacks to information. ICT applications, such as e-government, e-commerce, e-education, e-health and e-environment, are seen as enablers for development, as they provide an efficient channel to deliver a wide range of basic services in remote and rural areas. ICT applications can facilitate the achievement of millennium development
ICT applications, such as e-government 12, e-commerce 13, e-education 14, e-health 15 and e-environment, are seen as enablers for development, as they provide an efficient channel to deliver a wide range of basic services in remote and rural areas. ICT applications can facilitate the achievement of … 27/11/2019 · Practical Ecommerce is an independent, family-owned, online magazine in Traverse City, Michigan, U.S. We are not affiliated with any e-commerce service, platform, or provider. Our mission is to publish honest, authoritative articles, commentary, seminars, and podcasts to help online merchants.
Response Team will subscribe to various security industry alert services to keep abreast of relevant threats, vulnerabilities or alerts from actual incidents. Incident Response Team Members . Each of the following members will have a primary role in incident response. Information Technology Director / Chief Information Security Officer • Jan. 2015: GrillParts.com – Their e-commerce website was breached from Jan 2014 – Oct 2014 and exposed customer information, including names, addresses, and credit card numbers. • Dec. 2014: ABM Parking Services – Vendor supplied and maintained POS terminals were hacked and exposed customer information including credit card data.
Those are among the key findings of the February 2016 Cybersecurity Challenges, Risks, Trends, and Impacts Survey. Two hundred and twenty-five business and IT executives, directors, managers, and other leaders participated in the online survey, which was conducted by MIT Technology Review in partnership Intergovernmental Group of Experts on E-Commerce and the Digital Economy First session 4-6 October 2017 Geneva Contribution by FOUNDATION FOR ENTREPRENEURIAL ENHANCEMENT AND PROMOTION The views expressed are those of the author and do not necessarily reflect the views of UNCTAD.
Critical thinking tactics for nurses box 5-4, human nature lord of the flies essay. Title examples for research papers marketing analytics case study pdf, how to keep our environment clean essay in hindi: essay on the problem of child labour in india. 6 / Combating Cybersecurity Challenges with Advanced Analytics Digital Systems & Technology example, was about $300 million.8 Indirect costs resulting from organizational resources spent notifying victims and investigating the incident, as well as the loss of goodwill and customer churn, also have
21/11/2019 · Setting up an E-commerce system is a complex process and subject to many market specific variables. To maintain the integrity of the E-commerce system, testing becomes compulsory. It … the internet for mission-critical applications – from managing smart cities and operating power grids to conducting banking transactions and manufacturing connected vehicles – cybersecurity continues to remain a top imperative across the world. Unfortunately, …
Hacking the NFC credit cards for fun and debit )
Intergovernmental Group of Experts on E-Commerce and the. GBHackers on security is a Cyber Security platform that covers daily Cyber Security News, Hacking News, Technology updates and Kali Linux tutorials. Our mission is to keep the community up to date with happenings in the Cyber World., I have written this book for the people who already have an e-commerce site, i.e., an online store. Of course, there may be a few interesting subjects for the newcomers as well, but when I chose which topics to write about, I opted for the ones which would be attractive to companies that are interested in e-commerce and the growth stage..
Hacking the NFC credit cards for fun and debit ). tain a critical perspective on e-commerce and avoid industry hyperbole. Some of the important concepts from economics and marketing that we use to explore e-commerce are transaction cost, network externalities, information asymme-try, social networks, perfect digital markets, segmentation, price dispersion, targeting, and positioning., Many e-commerce sites directly ask users for personal information through forms. However, in addition to such information, many sites also record data about their users' browsing habits. This data can be matched with personal and demographic information to create a profile of user preferences..
the black box of e-commerce
Security Incident Response Plan WOU Homepage. 6 / Combating Cybersecurity Challenges with Advanced Analytics Digital Systems & Technology example, was about $300 million.8 Indirect costs resulting from organizational resources spent notifying victims and investigating the incident, as well as the loss of goodwill and customer churn, also have https://en.m.wikipedia.org/wiki/Digital_citizen (including scoping the test, critical systems to test, application and network-layer test inclusions, etc.). The document then moves on to practical guidance on selecting a penetration tester, methodologies that are used before, during, and after a test, guidelines for reporting and evaluating test results. The document concludes.
Critical thinking tactics for nurses box 5-4, human nature lord of the flies essay. Title examples for research papers marketing analytics case study pdf, how to keep our environment clean essay in hindi: essay on the problem of child labour in india. RESEARCH METHODOLOGY: TOOLS AND TECHNIQUES Bridge Center After framing hypothesis we have to prepare a research design i.e. we have to state the conceptual structure within which research would be conducted. The preparation of such a design facilitates research to be as
21/11/2019 · Setting up an E-commerce system is a complex process and subject to many market specific variables. To maintain the integrity of the E-commerce system, testing becomes compulsory. It … Many e-commerce sites directly ask users for personal information through forms. However, in addition to such information, many sites also record data about their users' browsing habits. This data can be matched with personal and demographic information to create a profile of user preferences.
Further attacks on U.S. critical energy infrastructure are expected, as nation states view disruption of the U.S. economy as a potential target.7 This report discusses the current state of electric grid cybersecurity, and the interconnected dependency of critical infrastructure with regard to electric sector reliability. Current efforts to E-commerce. The volume of B2B e-commerce has been overtaken in the last five years by the growth of consumer e-commerce applications as the general public (B2C) increasingly conduct business over networks with commercial and public sector organisations.
and trust in e-services and e-business, in particular. Background The Most Significant Cyber Challenges and Threats are: Threat of Penetrating and Sabotaging ICT Infrastructure New types of extremely serious cyberattacks have recently emerged, aimed at disrupting critical services, and deploying malware and viruses to destroy or disrupt 6 / Combating Cybersecurity Challenges with Advanced Analytics Digital Systems & Technology example, was about $300 million.8 Indirect costs resulting from organizational resources spent notifying victims and investigating the incident, as well as the loss of goodwill and customer churn, also have
criminal activity, these include hacking, cyber vandalism (defacement), dissemination of viruses, denial of service attacks, and domain name hijacking. The research community also has made many attempts to prevent and detect online criminal activity, Massa & Valverde [5] created a online fraud detection system for e-commerce applications The Top 5 e-Commerce Security Trends of 2019 Retailers can't be successful with a brick-and-mortar model only, and must embrace the omnichannel approach to drive growth and revenue while also improving customer engagement.
Many e-commerce sites directly ask users for personal information through forms. However, in addition to such information, many sites also record data about their users' browsing habits. This data can be matched with personal and demographic information to create a profile of user preferences. Hacking the NFC credit cards for fun and debit ;) Renaud Lifchitz – BT Read victim's card data and use it on e-commerce websites: CVV is not always other critical protective measures. This comprehensive standard is intended to help organizations proactively protect customer
tain a critical perspective on e-commerce and avoid industry hyperbole. Some of the important concepts from economics and marketing that we use to explore e-commerce are transaction cost, network externalities, information asymme-try, social networks, perfect digital markets, segmentation, price dispersion, targeting, and positioning. Those are among the key findings of the February 2016 Cybersecurity Challenges, Risks, Trends, and Impacts Survey. Two hundred and twenty-five business and IT executives, directors, managers, and other leaders participated in the online survey, which was conducted by MIT Technology Review in partnership
Critical Investigation Questions Questions you should have answers to during the investigation - How did the attacker gain initial access to the environment? - How did the attacker maintain access to the environment? - What is the storyline of the attack? - What data was stolen from the environment? - Have you contained the incident? tain a critical perspective on e-commerce and avoid industry hyperbole. Some of the important concepts from economics and marketing that we use to explore e-commerce are transaction cost, network externalities, information asymme-try, social networks, perfect digital markets, segmentation, price dispersion, targeting, and positioning.
Intergovernmental Group of Experts on E-Commerce and the Digital Economy First session 4-6 October 2017 Geneva Contribution by FOUNDATION FOR ENTREPRENEURIAL ENHANCEMENT AND PROMOTION The views expressed are those of the author and do not necessarily reflect the views of UNCTAD. E-commerce. The volume of B2B e-commerce has been overtaken in the last five years by the growth of consumer e-commerce applications as the general public (B2C) increasingly conduct business over networks with commercial and public sector organisations.
RESEARCH METHODOLOGY: TOOLS AND TECHNIQUES Bridge Center After framing hypothesis we have to prepare a research design i.e. we have to state the conceptual structure within which research would be conducted. The preparation of such a design facilitates research to be as • Jan. 2015: GrillParts.com – Their e-commerce website was breached from Jan 2014 – Oct 2014 and exposed customer information, including names, addresses, and credit card numbers. • Dec. 2014: ABM Parking Services – Vendor supplied and maintained POS terminals were hacked and exposed customer information including credit card data.
Many e-commerce sites directly ask users for personal information through forms. However, in addition to such information, many sites also record data about their users' browsing habits. This data can be matched with personal and demographic information to create a profile of user preferences. (including scoping the test, critical systems to test, application and network-layer test inclusions, etc.). The document then moves on to practical guidance on selecting a penetration tester, methodologies that are used before, during, and after a test, guidelines for reporting and evaluating test results. The document concludes
National Cybersecurity Strategy
E-commerce critical success factors East vs. West. Secure Alternative to Whatsapp for Retail and E-Commerce Enterprises Whatsapp is widely used by employees in retail and e-commerce enterprises as part of the shadow IT, if there is no enterprise messaging app with similar features like Teamwire in place. Teamwire offers a secure alternative to Whatsapp for retail and e-commerce enterprises., Those are among the key findings of the February 2016 Cybersecurity Challenges, Risks, Trends, and Impacts Survey. Two hundred and twenty-five business and IT executives, directors, managers, and other leaders participated in the online survey, which was conducted by MIT Technology Review in partnership.
Introduction to Information Security
eCommerce Testing How to Test an E-Commerce Website. Secure Alternative to Whatsapp for Retail and E-Commerce Enterprises Whatsapp is widely used by employees in retail and e-commerce enterprises as part of the shadow IT, if there is no enterprise messaging app with similar features like Teamwire in place. Teamwire offers a secure alternative to Whatsapp for retail and e-commerce enterprises., 1/3/2004 · Anatomy of a Web Services Attack A GUIDE TO THREATS AND PREVENTATIVE COUNTERMEASURES Forum Systems, Inc. e-commerce purchases. Web Services also enable enterprises and organizations to synergistically builds the response message and then sends the response (or a fault message) back to the client. Any legacy application or architecture.
Learning Objectives Upon completion of this material, you should be able to: • Define key terms and critical concepts of information security. • List the key challenges of information security, and key protection layers. • Describe the CNSS security model (McCumber Cube). • Be able to differentiate between threats and attacks to information. (including scoping the test, critical systems to test, application and network-layer test inclusions, etc.). The document then moves on to practical guidance on selecting a penetration tester, methodologies that are used before, during, and after a test, guidelines for reporting and evaluating test results. The document concludes
threatens critical infrastructure if it gets into the hospital IT systems, patients can die, if it gets into our power ground commerce market is very similar to a typical C2B or B2B marketplace – examples from the past include In response to these relentless threats the industry has come to the realisation that they need to change the Learning Objectives Upon completion of this material, you should be able to: • Define key terms and critical concepts of information security. • List the key challenges of information security, and key protection layers. • Describe the CNSS security model (McCumber Cube). • Be able to differentiate between threats and attacks to information.
• Jan. 2015: GrillParts.com – Their e-commerce website was breached from Jan 2014 – Oct 2014 and exposed customer information, including names, addresses, and credit card numbers. • Dec. 2014: ABM Parking Services – Vendor supplied and maintained POS terminals were hacked and exposed customer information including credit card data. The Top 5 e-Commerce Security Trends of 2019 Retailers can't be successful with a brick-and-mortar model only, and must embrace the omnichannel approach to drive growth and revenue while also improving customer engagement.
Micro, small, and medium-sized enterprises and e-commerce Richard Hill1, December 2017 There is no question that e-commerce and the digital economy pose challenges and offer opportunities for micro, small, and medium-sized enterprises (MSMEs). In the World Trade Organization (WTO), some Those are among the key findings of the February 2016 Cybersecurity Challenges, Risks, Trends, and Impacts Survey. Two hundred and twenty-five business and IT executives, directors, managers, and other leaders participated in the online survey, which was conducted by MIT Technology Review in partnership
the internet for mission-critical applications – from managing smart cities and operating power grids to conducting banking transactions and manufacturing connected vehicles – cybersecurity continues to remain a top imperative across the world. Unfortunately, … threatens critical infrastructure if it gets into the hospital IT systems, patients can die, if it gets into our power ground commerce market is very similar to a typical C2B or B2B marketplace – examples from the past include In response to these relentless threats the industry has come to the realisation that they need to change the
6 / Combating Cybersecurity Challenges with Advanced Analytics Digital Systems & Technology example, was about $300 million.8 Indirect costs resulting from organizational resources spent notifying victims and investigating the incident, as well as the loss of goodwill and customer churn, also have E-commerce. The volume of B2B e-commerce has been overtaken in the last five years by the growth of consumer e-commerce applications as the general public (B2C) increasingly conduct business over networks with commercial and public sector organisations.
RESEARCH METHODOLOGY: TOOLS AND TECHNIQUES Bridge Center After framing hypothesis we have to prepare a research design i.e. we have to state the conceptual structure within which research would be conducted. The preparation of such a design facilitates research to be as Learning Objectives Upon completion of this material, you should be able to: • Define key terms and critical concepts of information security. • List the key challenges of information security, and key protection layers. • Describe the CNSS security model (McCumber Cube). • Be able to differentiate between threats and attacks to information.
To explore web-based electronic commerce opportunities, Riggins presents a framework that identifies 15 key ways to add value to an organization's e-commerce strategy. The extent to which each of these is utilized represents critical success factors. threatens critical infrastructure if it gets into the hospital IT systems, patients can die, if it gets into our power ground commerce market is very similar to a typical C2B or B2B marketplace – examples from the past include In response to these relentless threats the industry has come to the realisation that they need to change the
to the IT budget: e-commerce: If a business critical cyber-incident were to occur (a hacking event preventing the use of critical business systems for example), how long would An incident response plan or disaster recovery plan Yes No (b) A business continuity plan Yes No If yes, has either of these plans been tested in the last 12 21/11/2019 · Setting up an E-commerce system is a complex process and subject to many market specific variables. To maintain the integrity of the E-commerce system, testing becomes compulsory. It …
21/11/2019 · Setting up an E-commerce system is a complex process and subject to many market specific variables. To maintain the integrity of the E-commerce system, testing becomes compulsory. It … CYBERCRIME • Cybercrime has surpassed drug trafficking as the most lucrative crime. • Almost anybody who is an active computer/ online user would have been a cybercrime
ICT applications, such as e-government 12, e-commerce 13, e-education 14, e-health 15 and e-environment, are seen as enablers for development, as they provide an efficient channel to deliver a wide range of basic services in remote and rural areas. ICT applications can facilitate the achievement of … 24/4/2019 · Hacking The Digital Experience Landscape Erdem İlhan, Deloitte Digital Webrazzi Dijital 2019 Slideshare uses cookies to improve functionality and performance, and to …
Penetration Testing Guidance
Hacking the NFC credit cards for fun and debit ). With the emerging fields in e-commerce, financial and identity information are at a higher risk of being stolen. The purpose of this paper is to illustrate a common cum valiant security threat to which most systems are prone to i.e. Session Hijacking. Sensitive user information are constantly transported between sessions after, 21/11/2019 · Setting up an E-commerce system is a complex process and subject to many market specific variables. To maintain the integrity of the E-commerce system, testing becomes compulsory. It ….
E-commerce critical success factors East vs. West. Micro, small, and medium-sized enterprises and e-commerce Richard Hill1, December 2017 There is no question that e-commerce and the digital economy pose challenges and offer opportunities for micro, small, and medium-sized enterprises (MSMEs). In the World Trade Organization (WTO), some, Response Team will subscribe to various security industry alert services to keep abreast of relevant threats, vulnerabilities or alerts from actual incidents. Incident Response Team Members . Each of the following members will have a primary role in incident response. Information Technology Director / Chief Information Security Officer.
E-commerce
State of the Hack. ICT applications, such as e-government 12, e-commerce 13, e-education 14, e-health 15 and e-environment, are seen as enablers for development, as they provide an efficient channel to deliver a wide range of basic services in remote and rural areas. ICT applications can facilitate the achievement of … https://en.m.wikipedia.org/wiki/Payment_Card_Industry_Data_Security_Standard 6 / Combating Cybersecurity Challenges with Advanced Analytics Digital Systems & Technology example, was about $300 million.8 Indirect costs resulting from organizational resources spent notifying victims and investigating the incident, as well as the loss of goodwill and customer churn, also have.
Those are among the key findings of the February 2016 Cybersecurity Challenges, Risks, Trends, and Impacts Survey. Two hundred and twenty-five business and IT executives, directors, managers, and other leaders participated in the online survey, which was conducted by MIT Technology Review in partnership CYBERCRIME • Cybercrime has surpassed drug trafficking as the most lucrative crime. • Almost anybody who is an active computer/ online user would have been a cybercrime
to the IT budget: e-commerce: If a business critical cyber-incident were to occur (a hacking event preventing the use of critical business systems for example), how long would An incident response plan or disaster recovery plan Yes No (b) A business continuity plan Yes No If yes, has either of these plans been tested in the last 12 (including scoping the test, critical systems to test, application and network-layer test inclusions, etc.). The document then moves on to practical guidance on selecting a penetration tester, methodologies that are used before, during, and after a test, guidelines for reporting and evaluating test results. The document concludes
6 / Combating Cybersecurity Challenges with Advanced Analytics Digital Systems & Technology example, was about $300 million.8 Indirect costs resulting from organizational resources spent notifying victims and investigating the incident, as well as the loss of goodwill and customer churn, also have I have written this book for the people who already have an e-commerce site, i.e., an online store. Of course, there may be a few interesting subjects for the newcomers as well, but when I chose which topics to write about, I opted for the ones which would be attractive to companies that are interested in e-commerce and the growth stage.
• Jan. 2015: GrillParts.com – Their e-commerce website was breached from Jan 2014 – Oct 2014 and exposed customer information, including names, addresses, and credit card numbers. • Dec. 2014: ABM Parking Services – Vendor supplied and maintained POS terminals were hacked and exposed customer information including credit card data. CYBERCRIME • Cybercrime has surpassed drug trafficking as the most lucrative crime. • Almost anybody who is an active computer/ online user would have been a cybercrime
The Top 5 e-Commerce Security Trends of 2019 Retailers can't be successful with a brick-and-mortar model only, and must embrace the omnichannel approach to drive growth and revenue while also improving customer engagement. threatens critical infrastructure if it gets into the hospital IT systems, patients can die, if it gets into our power ground commerce market is very similar to a typical C2B or B2B marketplace – examples from the past include In response to these relentless threats the industry has come to the realisation that they need to change the
threatens critical infrastructure if it gets into the hospital IT systems, patients can die, if it gets into our power ground commerce market is very similar to a typical C2B or B2B marketplace – examples from the past include In response to these relentless threats the industry has come to the realisation that they need to change the To explore web-based electronic commerce opportunities, Riggins presents a framework that identifies 15 key ways to add value to an organization's e-commerce strategy. The extent to which each of these is utilized represents critical success factors.
Secure Alternative to Whatsapp for Retail and E-Commerce Enterprises Whatsapp is widely used by employees in retail and e-commerce enterprises as part of the shadow IT, if there is no enterprise messaging app with similar features like Teamwire in place. Teamwire offers a secure alternative to Whatsapp for retail and e-commerce enterprises. and trust in e-services and e-business, in particular. Background The Most Significant Cyber Challenges and Threats are: Threat of Penetrating and Sabotaging ICT Infrastructure New types of extremely serious cyberattacks have recently emerged, aimed at disrupting critical services, and deploying malware and viruses to destroy or disrupt
Critical thinking tactics for nurses box 5-4, human nature lord of the flies essay. Title examples for research papers marketing analytics case study pdf, how to keep our environment clean essay in hindi: essay on the problem of child labour in india. Intergovernmental Group of Experts on E-Commerce and the Digital Economy First session 4-6 October 2017 Geneva Contribution by FOUNDATION FOR ENTREPRENEURIAL ENHANCEMENT AND PROMOTION The views expressed are those of the author and do not necessarily reflect the views of UNCTAD.
ICT applications, such as e-government 12, e-commerce 13, e-education 14, e-health 15 and e-environment, are seen as enablers for development, as they provide an efficient channel to deliver a wide range of basic services in remote and rural areas. ICT applications can facilitate the achievement of … Micro, small, and medium-sized enterprises and e-commerce Richard Hill1, December 2017 There is no question that e-commerce and the digital economy pose challenges and offer opportunities for micro, small, and medium-sized enterprises (MSMEs). In the World Trade Organization (WTO), some
CYBERCRIME • Cybercrime has surpassed drug trafficking as the most lucrative crime. • Almost anybody who is an active computer/ online user would have been a cybercrime • Jan. 2015: GrillParts.com – Their e-commerce website was breached from Jan 2014 – Oct 2014 and exposed customer information, including names, addresses, and credit card numbers. • Dec. 2014: ABM Parking Services – Vendor supplied and maintained POS terminals were hacked and exposed customer information including credit card data.
to the IT budget: e-commerce: If a business critical cyber-incident were to occur (a hacking event preventing the use of critical business systems for example), how long would An incident response plan or disaster recovery plan Yes No (b) A business continuity plan Yes No If yes, has either of these plans been tested in the last 12 aftermath of an attack is perceived as a critical risk to firms. In addition, as a key enabler of economic and social development, the banking sector needs to think about the critical infrastructure nature of its operations. PwC report that nearly 60 per cent of firms identify the speed of technological change as a threat to their growth